
step 1Visit the website
First you need to visit this site, see the left side that says "Find out if you can run that game on your PC"? click the button underneath it that says "Can YOU run it?"
First you need to visit this site, see the left side that says "Find out if you can run that game on your PC"? click the button underneath it that says "Can YOU run it?"
step 2Test your computer
Now to test your computer for compatibility. From the drop-down list, select the game that you wish to run. After you selected your game, click the "Can you RUN it" button. This will take you to a new page.
Now to test your computer for compatibility. From the drop-down list, select the game that you wish to run. After you selected your game, click the "Can you RUN it" button. This will take you to a new page.
step 3Analyzing data and results
This next page will analyze the data, if you are a Windows Vista user then UAC(User Account Control) will pop up and ask for permission, click yes as this is not harmful. Now your results will appear...It appears that I failed...:(
This next page will analyze the data, if you are a Windows Vista user then UAC(User Account Control) will pop up and ask for permission, click yes as this is not harmful. Now your results will appear...It appears that I failed...:(
step 4Finish
Well now you know how to check to see if you can run your game without having to drive all the way to the Local Generic Superstore near you, buy the game, wait 45 minutes to install it, find out that it won't run, and then run back to the store to return it. So I hope that I helped, and saved you the hassle of the return.
Well now you know how to check to see if you can run your game without having to drive all the way to the Local Generic Superstore near you, buy the game, wait 45 minutes to install it, find out that it won't run, and then run back to the store to return it. So I hope that I helped, and saved you the hassle of the return.

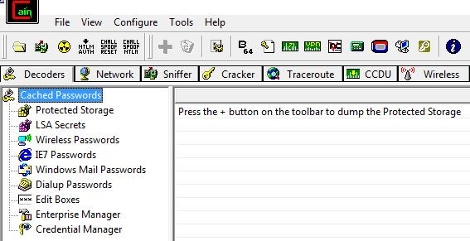
 Alternatively, you can use
Alternatively, you can use 
















 .
.
